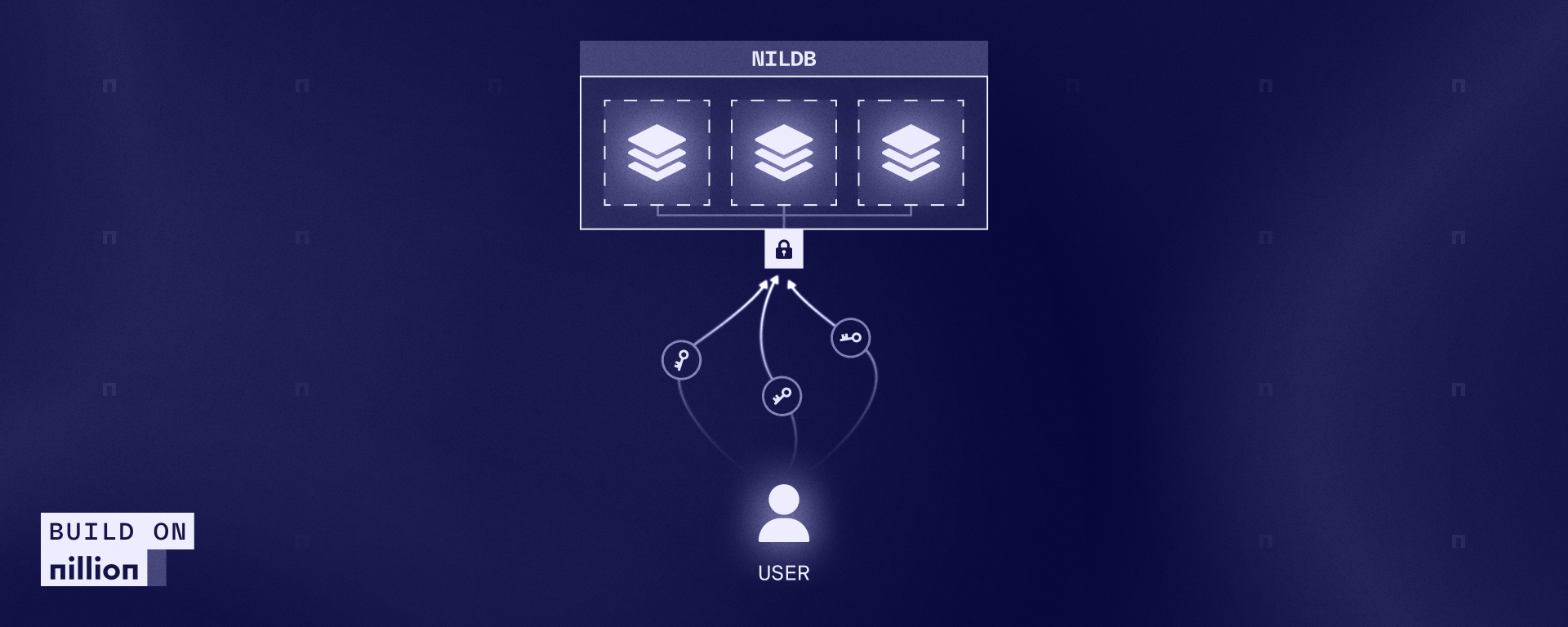
NilDB is Nillion’s secure, decentralized database that is purpose-built for privacy-preserving applications. It allows users to store data either encrypted (via symmetric or homomorphic encryption) or secret-shared (via MPC) across a cluster of nodes. These nodes form the Blind Module, a foundational component of Nillion’s SecretVault. Developers can choose to interact with any subset of nilDB clusters and nodes (as shown in the image below) and easily encrypt or secret-share data before uploading it. This creates a zero-trust architecture in which the backend never accesses plaintext and remains oblivious to the existence of other nodes.

Figure 1: nilDB architectural node diagram with various nodes and schemas
Fully Homomorphic Encryption (FHE) allows computations to be performed directly on encrypted data without requiring decryption. It is incredibly useful in client/server scenarios, where a user wants to offload computation to an untrusted server but does not want to reveal their raw data. In these settings, users generate key pairs (public and secret keys), encrypt their data with the public key, send it to the server for blind computation, and at the end, decrypt the result locally. Throughout this process, the server learns nothing about the client’s inputs and outputs.
But here’s the problem: key management is hard. Storing secret keys securely across devices (say, encrypting data on a laptop and decrypting results on a different device) becomes a major usability hurdle. Public keys, parameters, and serialization formats differ across libraries, and each library supports multiple schemes (e.g., CKKS for approximate computation, TFHE for bitwise, BGV/BFV for integers), further complicating things. Additionally, certain schemes introduce the need for multiple types of keys to support different operations (e.g., public keys for encryption, secret keys for decryption, relinearization keys for efficient multiplications, Galois keys for rotations, etc.). Key management dictates how and for how much a third party can manipulate ciphertexts. For example, not having access to the relinearization keys highly limits the types of algorithms that someone can execute on a ciphertext and the ability to decrypt it. At the same time, a user might want to outsource different computations to different FHE servers while maintaining the same keys.
A robust key management system is required to ensure security and usability, especially in a distributed setting. However, a single point of compromise could expose all keys, leading to potential data breaches. This necessitates a decentralized approach to key management and access control, which nilDB effectively provides. NilDB gives you a secure, decentralized way to store and retrieve your FHE keys and parameters, accessible from anywhere, without compromising on privacy. Need to share encrypted results between devices? Done. Utilizing a decentralized authorization network, users can be granted specific permissions based on their roles and responsibilities. For instance, some users may only receive public keys for encryption, while others may be authorized to obtain Galois keys for secure data transformations. The decentralized authorization network ensures that no unauthorized entity can escalate its privileges without explicit consent. Instead of entrusting a single party with security-critical functions, nilDB distributes trust among multiple entities. Ultimately, even if one node is compromised, the attacker gains no useful information without access to multiple other key shares, making data breaches computationally infeasible.
To demonstrate the ease of use of nilDB for FHE storage, we built fhe-on-nildb, a proof of concept that supports generating FHE keys using Microsoft SEAL (with CKKS), TFHE-rs (TFHE), and Lattigo (with BGV) and storing them directly in nilDB. You can save and retrieve public and secret keys, along with the parameters used for key generation. By distributing encryption keys and enforcing granular permission management, nilDB ensures that cryptographic operations remain both secure and efficient. The repository is implemented using SecretVault’s Python SDK and shows how to integrate various FHE schemes with nilDB.
This proof of concept shows how nilDB simplifies secure storage and management of private information, enabling seamless FHE key distribution and access control. NilDB enables privacy-enforced applications without the complexities of cryptography and infrastructure. As FHE adoption grows, solutions like nilDB pave the way for scalable, secure, and user-friendly implementations.
Follow @BuildOnNillion on X/Twitter for more updates like these